The National Security Agency (NSA) may have found a way to infect and reprogram hard drives all over the world, a highly complex attack that is undetectable and unremovable. The American Agency may have been doing this for more than a decade, under the guise of a group being called by researchers "Equation".
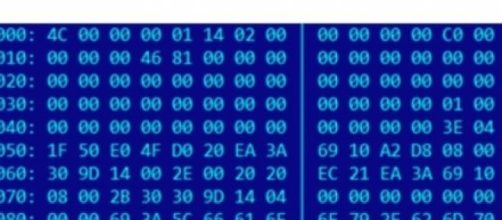
They use physical media, like CD-ROMs, USB sticks with exploits, web-based exploits and a self-replicating worm (Fanny) for their infection purposes. But the most surprising aspect of the group's technologies, one never before seen by researchers, is the ability to infect hard drive firmware.
Their code was discovered in hard drives from vendors such as Western Digital, Seagate, Toshiba, Samsung and Micron, among others. Their victims span over 30 countries, with most of the targets being governments and diplomatic institutions, military, telecommunication, nuclear research, oil and gas, mass media, Islamic activists and scholars, to name a few.
This is the outcome of a high profile investigation by Russian security software maker Kaspersky Lab, which uncovered a massive threat by what it calls the "Equation" group. They found at least 500 victims, from Iran to Russia (the two most targeted countries) Syria, Afghanistan, Kazakhstan and many others. But the ability of the spyware to self-destruct, indicates there may be a lot more victims; Kaspersky says as many as 2000 targets per month are infected.
"The Equation group is probably one of the most sophisticated cyber attack groups in the world; and they are the most advanced threat actor we have seen," Kaspersky Lab warns in its findings.
Let's be clear: Kaspersky Lab' researchers have not named the NSA nor the United States as the actors behind the so-called Equation attack group. But reading their findings, compiled in a FAQ document published on their SecureList blog, there is a clear link between one of Equation's techniques and those found on Stuxnet (a worm used by NSA to infect Iran's uranium enrichment facility in 2010).
"Some of the 'patients zero' of Stuxnet seem to have been infected by the Equation group. It is quite possible that the Equation group malware was used to deliver the Stuxnet payload," Kaspersky says.
Moreover, two former NSA employees have confirmed to Reuters that the NSA did develop this technique of hiding spyware in hard drives. The computer network exploitations by Equation group have been going on since 2001, maybe even before that (1996), using multiple malware tools.
But how did Kaspersky Lab uncover a cyber espionage operation that hid for the last 14 years? They were researching the operations of another malware attack, the Regin. "Somewhere in the Middle East, there is a computer we are calling 'The Magnet of Threats'," the researchers explain. This computer has been infected by Regin, Turla, ItaDuke, Animal Farm and Careto/Mask - all high profile attacks. When Kaspersky tried to analyze the Regin infection on this computer, they identified another module which did not appear to be part of the known infections. Hence, the discovery of the Equation group began. "The Equation group uses, some of which surpass the well-known "Regin" threat in complexity and sophistication," Kaspersky says.